Venus Protocol was attacked, but the attacker did not breach the system or hack anything; instead they used a smarter method?
.
On March 15, 2026 (Buddhist year 2569), Venus Protocol, a DeFi lending platform on the BNB Chain, was attacked, resulting in bad debt worth $2.18 million, approximately 75 million baht, which cannot be recovered (excluding other profits the attacker gained).
.
First, you need to understand how Venus works
Venus is a platform where users deposit crypto as collateral and can borrow other crypto, similar to using a house as a guarantee with a bank. If the collateral price drops sharply, the system will liquidate automatically, but if the price falls too quickly, the proceeds from the sale may be insufficient to cover the debt.
.
The attacker’s method is divided into 5 steps as follows
Step 1: Obtain funding without leaving traces
- The attacker brought in 7,400 ETH (≈$15 million) through Tornado Cash and used it as collateral on Aave to borrow about $9.92 million in stablecoins. The ETH remained intact, serving only as temporary collateral.
.
Step 2: Quietly accumulate $THE over 9 months (you could even call this step 0)
- Starting June 2025, the attacker gradually bought $THE, the low‑liquidity token of the Thena project, across multiple wallets until reaching 84 % of the 14.5 million supply cap set by Venus, without anyone noticing, while also opening a long position on a CEX betting that $THE price would rise.
.
Step 3: Bypass system constraints and pump $THE price
- Instead of using normal deposit channels, the attacker transferred $THE directly into a smart contract, bypassing the supply cap unnoticed. They then looped: depositing $THE, borrowing more $THE to buy more $THE, waiting for the oracle to update the price, and borrowing even more.
.
During this period two price levels appeared
- On DEXs, the attacker pumped $THE from $0.27 to almost $5.
- The oracle price used by Venus to value collateral rose from $0.27 to almost $0.53 before falling back to $0.24 after liquidation.
.
The timeline shows the events happened very quickly
- At 11:00 am, $THE in the protocol was 12.2 million tokens (84 % of the cap), still within limits.
- At 12:00 pm, it surged to 49.5 million tokens (341 % of the cap), exceeding the cap threefold.
- At 12:42 pm, it peaked at 53.2 million tokens (367 % of the cap) before liquidation.
.
Step 4: Borrow from Venus using inflated collateral price
- While the oracle price of $THE was artificially high, the attacker placed 36.1 million $THE as collateral on Venus through two wallets and borrowed assets.
- 2,172 BNB
- 1.516 million CAKE
- 20 BTC
.
Total value about $5.07 million (≈175 million baht), which was transferred out immediately.
.
Step 5: Open a short and dump $THE price. The attacker sold $THE on the CEX, driving the price back down to $0.24, close to the original level. The short position made a profit, but the collateral left on Venus was insufficient to cover the debt, and liquidation could not recover enough.
.
Thus a bad debt of $2.18 million remained for Venus to absorb.
.
How much did the attacker actually earn?
- Known from the blockchain:
- Approximately $5.07 million borrowed from Venus.
.
- Unknown and hard to estimate:
- Profit from the long position opened before the $THE pump on the CEX.
- Profit from the short position opened before the $THE dump on the CEX.
- These two parts are not recorded on the blockchain and cannot be audited.
.
The attacker’s real profit likely came mainly from those two parts, because $THE on the CEX moved from $0.27 to $0.6 and back to $0.24 in a single cycle. A sufficiently large position could generate several million dollars of profit without leaving any blockchain trace.
.
Venus responded by pausing borrowing and withdrawals of $THE immediately, and pausing six other high‑risk markets: $BCH, $LTC, $UNI, $AAVE, $FIL, and $TWT, and announced it would release a post‑mortem report with a detailed remediation plan.
.
For us, this case shows that DeFi risk is not only from hacks but also from design flaws, and attackers may plan up to nine months in advance. Low‑liquidity tokens used as collateral on large platforms are a perennial weak point that attackers seek.
 THE (THE)
THE (THE) OCT News Media Influencer C1.87K @news_oct
OCT News Media Influencer C1.87K @news_oct
 OCT News Media Influencer C1.87K @news_oct
OCT News Media Influencer C1.87K @news_oct 7 1 124 オリジナル >リリース後のTHEのトレンド非常に弱気
7 1 124 オリジナル >リリース後のTHEのトレンド非常に弱気 Bambambam OnChain_Analyst Community_Lead B2.79K @bambambebbam
Bambambam OnChain_Analyst Community_Lead B2.79K @bambambebbam Lookonchain OnChain_Analyst Media C680.82K @lookonchain
Lookonchain OnChain_Analyst Media C680.82K @lookonchain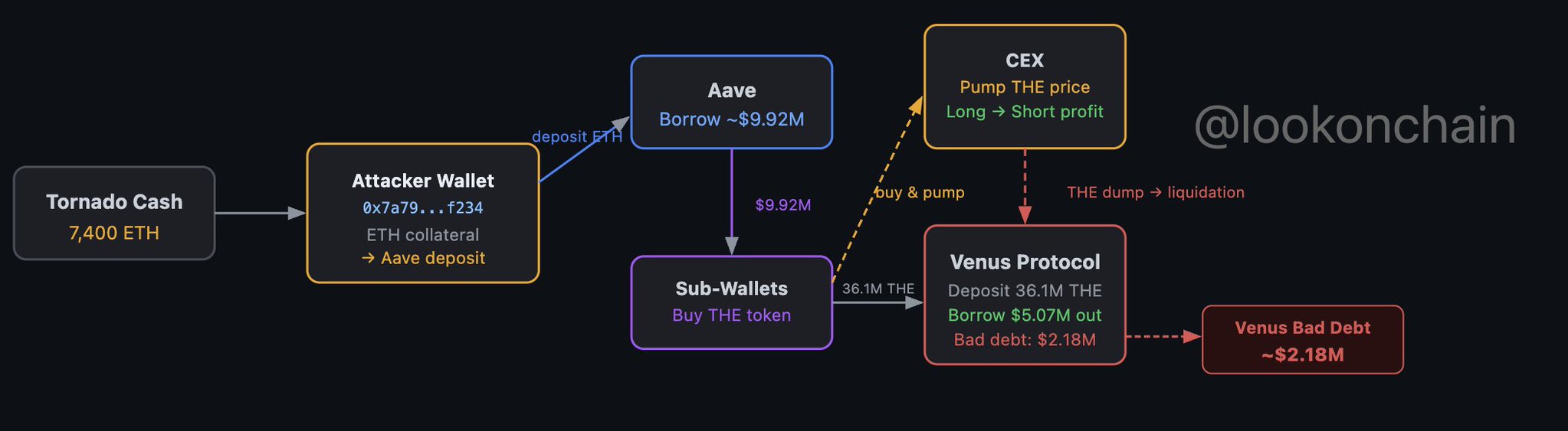 0 0 73 オリジナル >リリース後のTHEのトレンド非常に弱気
0 0 73 オリジナル >リリース後のTHEのトレンド非常に弱気 merp Trader OnChain_Analyst B45.26K @0xMerp
merp Trader OnChain_Analyst B45.26K @0xMerp Lookonchain OnChain_Analyst Media C680.82K @lookonchain
Lookonchain OnChain_Analyst Media C680.82K @lookonchain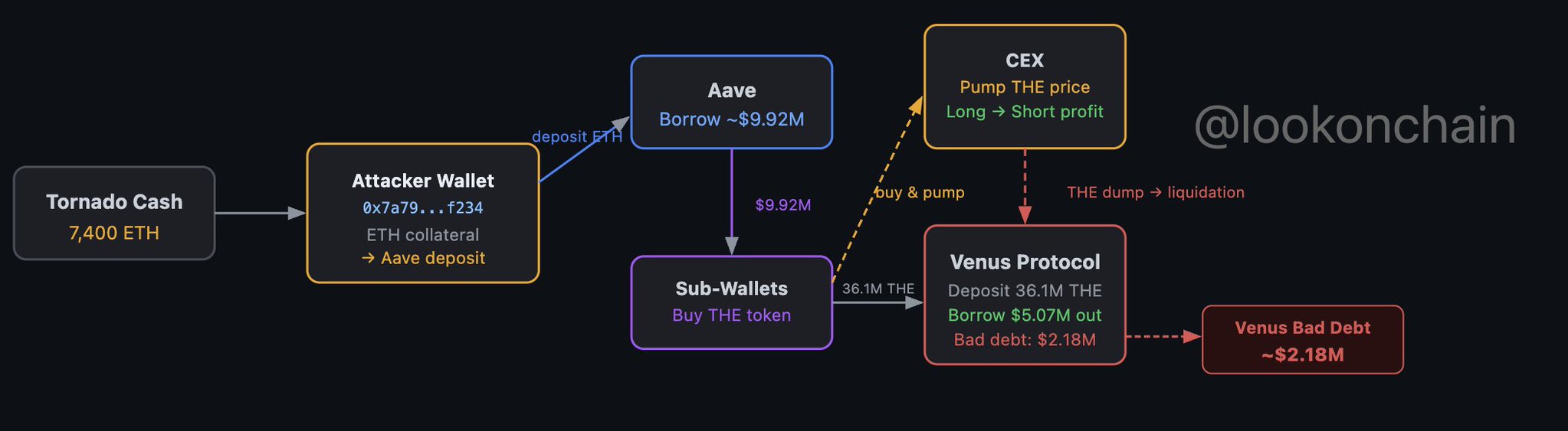 19 2 3.54K オリジナル >リリース後のTHEのトレンド非常に弱気
19 2 3.54K オリジナル >リリース後のTHEのトレンド非常に弱気